In such cases, the fraudster usually attempts to obtain sensitive information over a voice call. The fraudster normally tries to gain the victim’s trust by impersonating a credible individual such as a banking authority or a police investigation officer. Victims may not verify the received calls purportedly made by such persons thinking that the calls are from regulators, to avoid embarrassment or as a result of “warnings” given by the “officer".
Fake phone calls have been on the rise whereby scammers would trick customers into revealing their confidential banking credentials (such as login ID/password/NRIC, etc.) by following given instructions.
To know how to protect yourself against Phone Scams, please read the Notices below:
Spyware
Spyware is a software that enables a user to obtain covert information about another’s computer activities by transmitting data covertly from their hard drive. It is one of the most common threats on the internet. It can easily infect your device and it can be hard to identify. Spyware is a threat to businesses and individual users since it can steal sensitive information and harm your network.
You can recognise spyware on your device when it shows symptoms such as slow or crashes unexpectedly, running out of hard drive space and you are getting pop-ups when you are online or offline. If you think your device is affected, run a scan with your current security software and remove the spyware using the virus removal tool.
Embedded Links
Cybercriminals may use embedded links to lure you into clicking on them and upload malware to your device or network in order to collect your confidential information. Only click on the embedded link from trusted sources to avoid running the risk of malware being uploaded to your computer or network.
Pretext Calling

Also known as a “conformational call” or “pretence call” or “tapping” is a tape-recorded call between two people, usually between the victim and the suspect of the crime. The cyber-criminals may pretend to be bank officers to obtain your confidential information. Once obtained your confidential information, the cyber-criminals may be calling your bank to pose as you and perform transactions using your account.
Another form of pretext calling is when the cyber-criminals request for your confirmation on transactions that supposedly made with your credit card. When you inform cyber-criminals that you do not have such credit cards, you’re provided with a fake Bank Negara Malaysia telephone number in order to lodge a report. Upon calling, the cyber-criminals will request for confidential information which will subsequently be used for fraudulent activities.
Another type of pretext calling whereas the cyber-criminals will call up and pretend to call from a legal company, court, customs or police station. The cyber-criminals then state that you have an outstanding amount and needs to be paid on the same day. If you fall with their tactic, you will be forced to make payment to them over the phone. Do not trust such a call and always demand an official letter so that you can verify the statement.
Pharming
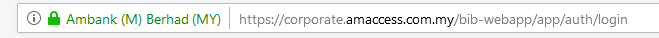
Pharming is the fraudulent practise of directing Internet users to a bogus website that mimics the appearance of a legitimate one, in order to obtain personal information such as passwords, account numbers and etc. It can be conducted either by changing the host file on your computer by the exploitation of a vulnerability in DNS server software. If you are accessing AmBank corporate internet banking, please ensure the website address has https:// in its URL.
Keylogging
Keylogging is the activity carried out by cyber-criminals using keylogger technology that tracks and records consecutive keystrokes on a keyboard. Also known as “Keyboard Capturing”, the users who use the keyboard for logging in to the online banking often unaware that their activities are being monitored. Keyloggers are used to gain fraudulent access to confidential information such as personal details, credit card data, access credentials, etc.
Protect your account by installing the anti-spyware applications which are able to detect and disable/cleanse keylogging software. AmBank corporate internet banking is secure from keylogging as each PIN is invalidated as soon as it is used.
Keylogging on ATM

Cybercriminals have been known to use keyboard overlays on ATMs to capture people’s PINs. Each keypress is registered by the keyboard of the ATM as well as the criminal’s keypad that is placed over it. The device is designed to look like an integrated part of the machine so that bank customers are unaware of its presence.
Cover the keypad with your hands when entering the PIN into an ATM or supermarket’s terminal. Some banks and supermarket’s terminal already equipped with a cover to prevent theft and some are not. Hiding your PIN when you use an ATM is a simple way to avoid nasty financial surprises in your bank account.
Keylogging on Mobile
The main purpose for cyber-criminals to keylogging on mobile phones is to capture and transmit information including email, SMS and keystrokes on mobile phones without the phone user knowing it.
SMS Scam
SMS scam usually involves SMSes initiated by a fraudster to trick victims into believing that they have won a contest/reward and which attempt to lead them into compromising their banking information and/or create an internet banking facility without the victim even realising it.
This type of scam may also involve ‘identity theft’ since an unauthorised person usually pretends to be a valid account holder and accesses the customer’s account (usually through the internet), unbeknown to the account holder.
Fake SMSes have been on the rise whereby scammers would trick customers into revealing their confidential banking credentials (such as login ID/password/NRIC, etc.) by following given instructions.
To know how to protect yourself against SMSes Scams, please read the Notices below: